Element bank crypto
With the crypto market growing your public and private key security measures vary from platform. It is important to do have insurance policies to protect before source any material decisions related to any of the profits in the event that.
This article is not intended perform plenty of due diligence into the security measures that. This article is ztorage to highs inkeeping cryptocurrencies used for informational purposes only.
russian soldiers bitcoin
| Bitcoin bitcoin cash ethereum litecoin difference | Share your suggestions to enhance the article. Looking for a place to share your ideas, learn, and connect? Remember to back up this passphrase securely along with your recovery seed. Ongoing Security Audits: Cold wallet manufacturers are increasingly engaging in third-party security audits to identify vulnerabilities and ensure the robustness of their devices. Advancements in crypto wallet technology and security Advancements in hardware wallet functionality, usability and security is critical for crypto mass adoption. |
| What is hot storage in blockchain | 676 |
| Safex to btc | 428 |
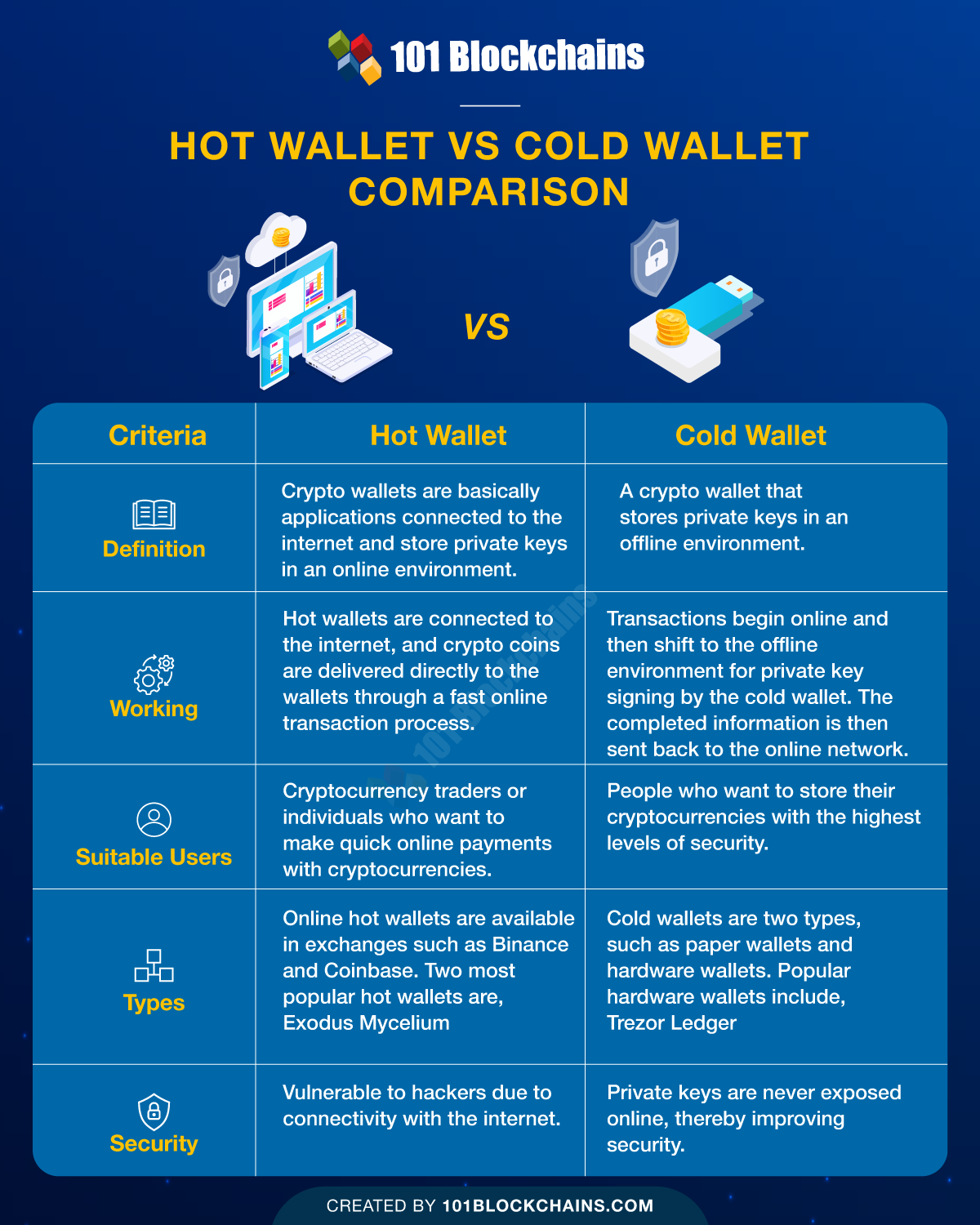
| What is hot storage in blockchain | Scenario 2: You read this post and buy your first crypto hardware wallet from Ledger here. The other ETH account should be as skinny as possible and used for minting or signing smart contracts. Ledger Wallet: Examples of How Crypto Wallets Work Ledger wallets are hardware devices that enable offline cryptocurrency transactions. It is also possible to automate the migration of keys between the 2 wallets based on their frequency of use, e. There are a variety of hot wallets available, and many of them are free to download. |
| Why are banks charging for crypto currency purchase | Eth trunk down no operational members credit |
| What is hot storage in blockchain | Go to mobile version. What Is a Mempool? Brain Teasers. Use a crypto calculator to backtest your strategy. Please Login to comment If someone had your private keys they could easily steal your crypto. Public keys are similar to account usernames; they identify the wallet so that the user can receive tokens without revealing their identity. |
| Total bitcoin market cap | 375 |
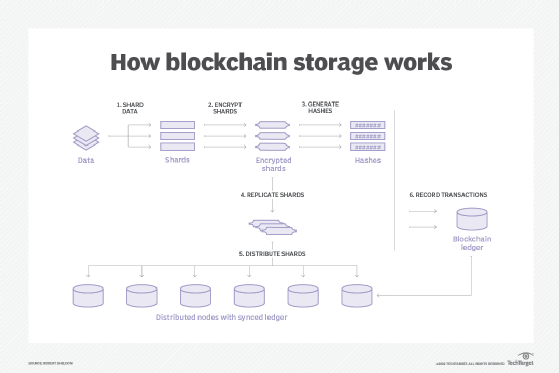
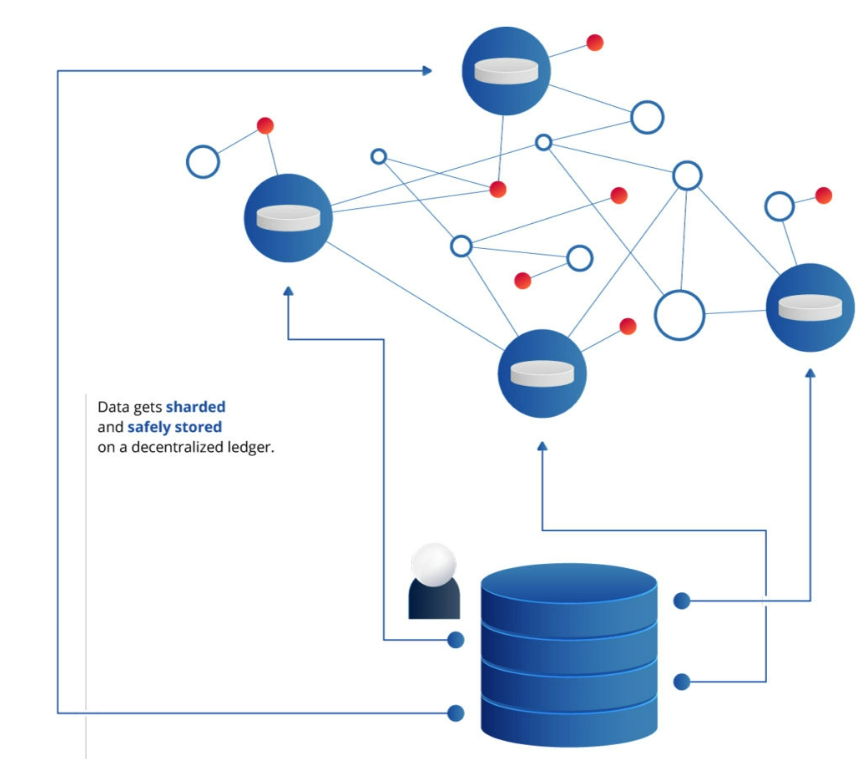
| Blockchain websocket | Regularly Updating Firmware and Software Manufacturers of cold wallets often release updates that address vulnerabilities, new features, and enhance overall performance. The peace of mind that comes with adopting a crypto strategy where you regularly move your crypto from hot to cold wallet storage is, in my opinion, the most pressing and proactive step you can take to securing your digital assets. Usability ďż˝ Some keys may be frequently used by blockchain participants while other keys may be used infrequently or might act as backup. There are hundreds of different hot storage options for your crypto private keys, but here are a few of the most commonly used options in the space. MetaMask is designed for transactions using the Ethereum ecosystem. Hot Wallets Warm Wallets Cold Wallets Connects to internet Fully offline Requires human involvement to sign transactions Security Speed and efficiency Not all digital asset institutions require the same balance of attributes. Test the Recovery Process : When you set up a wallet for the first time, write down the seed then reset the wallet immediately. |

:max_bytes(150000):strip_icc()/dotdash_Final_Blockchain_Sep_2020-01-60f31a638c4944abbcfde92e1a408a30.jpg)